Can anyone help me to get the setup right for a MikroTik router, I can not seem to work it out
Hey there!
Whats your config so far?
Also what Mikrotik do you have ![]()
So on the terminal run the following:
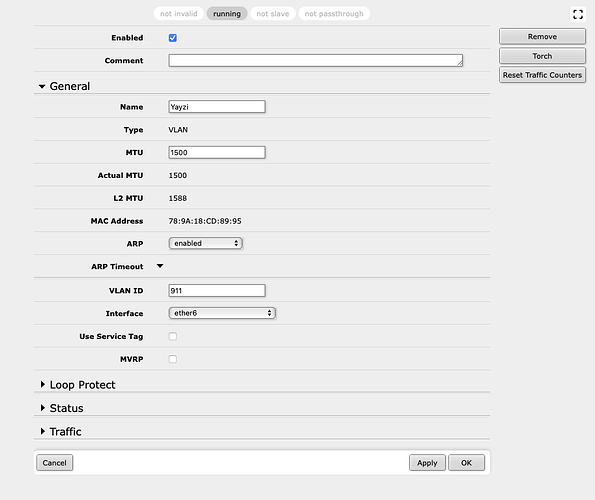
/interface vlan add name=vlan911 interface=ether6 vlan-id=911
/ip dhcp-client add interface=vlan911 use-peer-dns=yes add-default-route=yes
/ip firewall nat add chain=srcnat out-interface=vlan911 action=masquerade
If you havent setup any firewall rules etc do this as well (this is very basic so can be edited)
/ip firewall filter
add chain=input action=accept connection-state=established,related
add chain=input action=accept protocol=icmp
add chain=input action=drop in-interface=vlan911
add chain=forward action=accept connection-state=established,related
add chain=forward action=drop connection-state=invalid
Feel free to drop me a DM on the discord and ill help out where possible.
1 Like
@WhyAydan Just sent you a DM
Below config works for me and includes IPV6 setup.
You will need to adjust the WAN interface name for RB4011.
# 2024-12-10 17:00:42 by RouterOS 7.16
# WAN/LAN interfaces + vlan
/interface vlan
add interface=sfp-sfpplus1 name=citifibre-vlan vlan-id=911
/interface list
add name=WAN
add name=LAN
/ip neighbor discovery-settings
set discover-interface-list=LAN
/interface list member
add interface=bridge1 list=LAN
add interface=sfp-sfpplus1 list=WAN
add interface=citifibre-vlan list=WAN
/ip dhcp-client
add interface=citifibre-vlan use-peer-dns=no use-peer-ntp=no
# IPV4 Firewall
/ip firewall filter
add action=accept chain=input comment=\
"defconf: accept established,related,untracked" connection-state=\
established,related,untracked
add action=drop chain=input comment="defconf: drop invalid" connection-state=\
invalid
add action=accept chain=input comment="defconf: accept ICMP" protocol=icmp
add action=accept chain=input comment=\
"defconf: accept to local loopback (for CAPsMAN)" disabled=yes \
dst-address=127.0.0.1
add action=drop chain=input comment="defconf: drop all not coming from LAN" \
in-interface-list=!LAN
add action=accept chain=forward comment="defconf: accept in ipsec policy" \
ipsec-policy=in,ipsec
add action=accept chain=forward comment="defconf: accept out ipsec policy" \
ipsec-policy=out,ipsec
add action=fasttrack-connection chain=forward comment="defconf: fasttrack" \
connection-state=established,related hw-offload=yes
add action=accept chain=forward comment=\
"defconf: accept established,related, untracked" connection-state=\
established,related,untracked
add action=drop chain=forward comment="defconf: drop invalid" \
connection-state=invalid
add action=drop chain=forward comment=\
"defconf: drop all from WAN not DSTNATed" connection-nat-state=!dstnat \
connection-state=new in-interface-list=WAN
# IPV4 NAT
/ip firewall nat
add action=masquerade chain=srcnat comment="defconf: masquerade" \
out-interface-list=WAN
# Disable insecure services
/ip firewall service-port
set ftp disabled=yes
set tftp disabled=yes
set h323 disabled=yes
set sip disabled=yes
set pptp disabled=yes
/ip service
set telnet disabled=yes
set ftp disabled=yes
set api disabled=yes
# Yayzi IPV6
/ipv6 address
add eui-64=yes from-pool=yayzi-pool interface=\
bridge1
/ipv6 dhcp-client
add add-default-route=yes interface=citifibre-vlan pool-name=yayzi-pool \
pool-prefix-length=60 request=prefix use-peer-dns=no
/ipv6 firewall address-list
add address=::/128 comment="defconf: unspecified address" list=bad_ipv6
add address=::1/128 comment="defconf: lo" list=bad_ipv6
add address=fec0::/10 comment="defconf: site-local" list=bad_ipv6
add address=::ffff:0.0.0.0/96 comment="defconf: ipv4-mapped" list=bad_ipv6
add address=::/96 comment="defconf: ipv4 compat" list=bad_ipv6
add address=100::/64 comment="defconf: discard only " list=bad_ipv6
add address=2001:db8::/32 comment="defconf: documentation" list=bad_ipv6
add address=2001:10::/28 comment="defconf: ORCHID" list=bad_ipv6
add address=3ffe::/16 comment="defconf: 6bone" list=bad_ipv6
# IPV6 Firewall
/ipv6 firewall filter
add action=accept chain=input comment=\
"defconf: accept established,related,untracked" connection-state=\
established,related,untracked
add action=drop chain=input comment="defconf: drop invalid" connection-state=\
invalid
add action=accept chain=input comment="defconf: accept ICMPv6" protocol=icmpv6
add action=accept chain=input comment="defconf: accept UDP traceroute" port=\
33434-33534 protocol=udp
add action=accept chain=input comment=\
"defconf: accept DHCPv6-Client prefix delegation." dst-port=546 protocol=\
udp src-address=fe80::/10
add action=accept chain=input comment="defconf: accept IKE" dst-port=500,4500 \
protocol=udp
add action=accept chain=input comment="defconf: accept ipsec AH" protocol=\
ipsec-ah
add action=accept chain=input comment="defconf: accept ipsec ESP" protocol=\
ipsec-esp
add action=accept chain=input comment=\
"defconf: accept all that matches ipsec policy" ipsec-policy=in,ipsec
add action=drop chain=input comment=\
"defconf: drop everything else not coming from LAN" in-interface-list=!LAN
add action=accept chain=forward comment=\
"defconf: accept established,related,untracked" connection-state=\
established,related,untracked
add action=drop chain=forward comment="defconf: drop invalid" \
connection-state=invalid
add action=drop chain=forward comment=\
"defconf: drop packets with bad src ipv6" src-address-list=bad_ipv6
add action=drop chain=forward comment=\
"defconf: drop packets with bad dst ipv6" dst-address-list=bad_ipv6
add action=drop chain=forward comment="defconf: rfc4890 drop hop-limit=1" \
hop-limit=equal:1 protocol=icmpv6
add action=accept chain=forward comment="defconf: accept ICMPv6" protocol=\
icmpv6
add action=accept chain=forward comment="defconf: accept HIP" protocol=139
add action=accept chain=forward comment="defconf: accept IKE" dst-port=\
500,4500 protocol=udp
add action=accept chain=forward comment="defconf: accept ipsec AH" protocol=\
ipsec-ah
add action=accept chain=forward comment="defconf: accept ipsec ESP" protocol=\
ipsec-esp
add action=accept chain=forward comment=\
"defconf: accept all that matches ipsec policy" ipsec-policy=in,ipsec
add action=drop chain=forward comment=\
"defconf: drop everything else not coming from LAN" in-interface-list=!LAN
# IPV6 Neighbour Discovery
/ipv6 nd
set [ find default=yes ] interface=bridge1
I wiped out all my settings and used the ones above without the IPV6 (with a slight tweak as the connection is on ether 1.)
All that happened was that the status on the /IP DHCP-Client was searching
Going to repeat it in wider chat.
Below is a full config for RB4011 which works:
/interface bridge
add comment=defconf name=bridge \
port-cost-mode=short
/interface vlan
add interface=sfp-sfpplus1 name=citifibre-vlan vlan-id=911
/interface ethernet
set [ find default-name=ether1 ] comment="Virgin Gateway"
set [ find default-name=ether7 ] comment="Yayzi Gateway"
/interface list
add comment=defconf name=WAN
add comment=defconf name=LAN
/ip pool
add name=dhcp ranges=192.168.1.2-192.168.68.200
/ip dhcp-server
add address-pool=dhcp interface=bridge lease-time=10m name=defconf
/ip smb users
set [ find default=yes ] disabled=yes
/port
set 0 name=serial0
set 1 name=serial1
/interface bridge port
add bridge=bridge comment=defconf interface=ether2 internal-path-cost=10 \
path-cost=10
add bridge=bridge comment=defconf interface=ether3 internal-path-cost=10 \
path-cost=10
add bridge=bridge comment=defconf interface=ether4 internal-path-cost=10 \
path-cost=10
add bridge=bridge comment=defconf interface=ether5 internal-path-cost=10 \
path-cost=10
add bridge=bridge comment=defconf interface=ether6 internal-path-cost=10 \
path-cost=10
add bridge=bridge comment=defconf interface=ether8 internal-path-cost=10 \
path-cost=10
add bridge=bridge comment=defconf interface=ether9 internal-path-cost=10 \
path-cost=10
add bridge=bridge comment=defconf interface=ether10 internal-path-cost=10 \
path-cost=10
add bridge=bridge comment=defconf interface=sfp-sfpplus1 internal-path-cost=10 \
path-cost=10
/interface list member
add interface=bridge list=LAN
add interface=ether1 list=WAN
add interface=ether7 list=WAN
add interface=citifibre-vlan list=WAN
/ip address
add address=192.168.1.1/24 comment=defconf interface=bridge network=\
192.168.1.0
/ip neighbor discovery-settings
set discover-interface-list=LAN
/ip dhcp-server network
add address=192.168.1.0/24 comment=defconf dns-server=192.168.1.1 domain=lan \
gateway=192.168.1.1 netmask=24 ntp-server=192.168.1.1
/ip dns
set servers=8.8.8.8,8.8.4.4 allow-remote-requests=yes
/ip dns static
add address=192.168.1.1 comment=defconf name=router.lan
/ip dhcp-client
add interface=ether1 use-peer-dns=no use-peer-ntp=no comment="Virgin DHCP Client" default-route-distance=1
add interface=citifibre-vlan use-peer-dns=no use-peer-ntp=no comment="Yayzi DHCP Client" default-route-distance=2
/ip firewall filter
add action=accept chain=input comment=\
"defconf: accept established,related,untracked" connection-state=\
established,related,untracked
add action=drop chain=input comment="defconf: drop invalid" connection-state=\
invalid
add action=accept chain=input comment="defconf: accept ICMP" protocol=icmp
add action=accept chain=input comment=\
"defconf: accept to local loopback (for CAPsMAN)" disabled=yes \
dst-address=127.0.0.1
add action=drop chain=input comment="defconf: drop all not coming from LAN" \
in-interface-list=!LAN
add action=accept chain=forward comment="defconf: accept in ipsec policy" \
ipsec-policy=in,ipsec
add action=accept chain=forward comment="defconf: accept out ipsec policy" \
ipsec-policy=out,ipsec
add action=fasttrack-connection chain=forward comment="defconf: fasttrack" \
connection-state=established,related hw-offload=yes
add action=accept chain=forward comment=\
"defconf: accept established,related, untracked" connection-state=\
established,related,untracked
add action=drop chain=forward comment="defconf: drop invalid" \
connection-state=invalid
add action=drop chain=forward comment=\
"defconf: drop all from WAN not DSTNATed" connection-nat-state=!dstnat \
connection-state=new in-interface-list=WAN
/ip firewall nat
add action=masquerade chain=srcnat comment="defconf: masquerade" \
out-interface-list=WAN
/ip firewall service-port
set ftp disabled=yes
set tftp disabled=yes
set h323 disabled=yes
set sip disabled=yes
set pptp disabled=yes
/ip service
set telnet disabled=yes
set ftp disabled=yes
set api disabled=yes
/ipv6 address
add eui-64=yes from-pool=yayzi-pool interface=\
bridge
/ipv6 dhcp-client
add add-default-route=yes interface=citifibre-vlan pool-name=yayzi-pool \
pool-prefix-length=60 request=prefix use-peer-dns=no
/ipv6 firewall address-list
add address=::/128 comment="defconf: unspecified address" list=bad_ipv6
add address=::1/128 comment="defconf: lo" list=bad_ipv6
add address=fec0::/10 comment="defconf: site-local" list=bad_ipv6
add address=::ffff:0.0.0.0/96 comment="defconf: ipv4-mapped" list=bad_ipv6
add address=::/96 comment="defconf: ipv4 compat" list=bad_ipv6
add address=100::/64 comment="defconf: discard only " list=bad_ipv6
add address=2001:db8::/32 comment="defconf: documentation" list=bad_ipv6
add address=2001:10::/28 comment="defconf: ORCHID" list=bad_ipv6
add address=3ffe::/16 comment="defconf: 6bone" list=bad_ipv6
/ipv6 firewall filter
add action=accept chain=input comment=\
"defconf: accept established,related,untracked" connection-state=\
established,related,untracked
add action=drop chain=input comment="defconf: drop invalid" connection-state=\
invalid
add action=accept chain=input comment="defconf: accept ICMPv6" protocol=icmpv6
add action=accept chain=input comment="defconf: accept UDP traceroute" port=\
33434-33534 protocol=udp
add action=accept chain=input comment=\
"defconf: accept DHCPv6-Client prefix delegation." dst-port=546 protocol=\
udp src-address=fe80::/10
add action=accept chain=input comment="defconf: accept IKE" dst-port=500,4500 \
protocol=udp
add action=accept chain=input comment="defconf: accept ipsec AH" protocol=\
ipsec-ah
add action=accept chain=input comment="defconf: accept ipsec ESP" protocol=\
ipsec-esp
add action=accept chain=input comment=\
"defconf: accept all that matches ipsec policy" ipsec-policy=in,ipsec
add action=drop chain=input comment=\
"defconf: drop everything else not coming from LAN" in-interface-list=!LAN
add action=accept chain=forward comment=\
"defconf: accept established,related,untracked" connection-state=\
established,related,untracked
add action=drop chain=forward comment="defconf: drop invalid" \
connection-state=invalid
add action=drop chain=forward comment=\
"defconf: drop packets with bad src ipv6" src-address-list=bad_ipv6
add action=drop chain=forward comment=\
"defconf: drop packets with bad dst ipv6" dst-address-list=bad_ipv6
add action=drop chain=forward comment="defconf: rfc4890 drop hop-limit=1" \
hop-limit=equal:1 protocol=icmpv6
add action=accept chain=forward comment="defconf: accept ICMPv6" protocol=\
icmpv6
add action=accept chain=forward comment="defconf: accept HIP" protocol=139
add action=accept chain=forward comment="defconf: accept IKE" dst-port=\
500,4500 protocol=udp
add action=accept chain=forward comment="defconf: accept ipsec AH" protocol=\
ipsec-ah
add action=accept chain=forward comment="defconf: accept ipsec ESP" protocol=\
ipsec-esp
add action=accept chain=forward comment=\
"defconf: accept all that matches ipsec policy" ipsec-policy=in,ipsec
add action=drop chain=forward comment=\
"defconf: drop everything else not coming from LAN" in-interface-list=!LAN
/ipv6 nd
set [ find default=yes ] interface=bridge
/system clock
set time-zone-name=Europe/London
/system ntp client
set enabled=yes
/system ntp server
set enabled=yes
/system ntp client servers
add address=0.uk.pool.ntp.org
add address=1.uk.pool.ntp.org
add address=2.uk.pool.ntp.org
add address=3.uk.pool.ntp.org
/tool mac-server
set allowed-interface-list=LAN
/tool mac-server mac-winbox
set allowed-interface-list=LAN